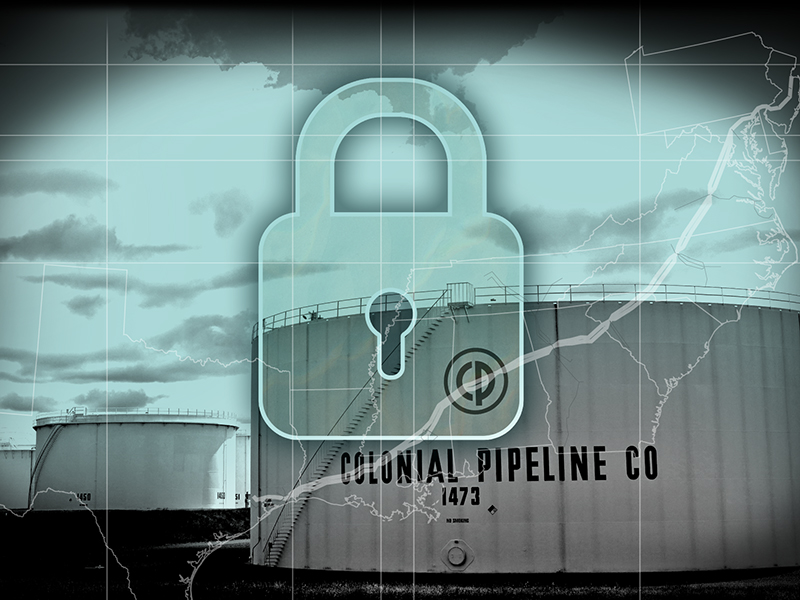
One of the nation’s largest pipelines was forced to shut down in early May 2021 after falling victim to a ransomware attack. The 5,500-mile pipeline is operated by Colonial Pipeline and carries refined gasoline and jet fuel from Texas to New York. This pipeline transports 45% of the east coast’s fuel supplies. There are some key takeaways from the Colonial Pipeline breach that we can learn from.
The attack—carried out by DarkSide ransomware—resulted in gas shortages along the east coast due to Colonial Pipeline halting their operations in an effort to contain the breach. DarkSide reportedly stole 100 gigabytes of data from Colonial Pipeline and allegedly threatened to leak portions of it to the public unless a $5 million ransom was paid. This method, known as double extortion, involves cybercriminals not only encrypting stolen data and making it inaccessible but also threatening to release it.
Key Takeaways from the Colonial Pipeline Breach
The shutdown served as a reminder and warning of the catastrophic impact ransomware can have on businesses—especially those with aging IT infrastructure—and people. There are a few key takeaways from the Colonial pipeline breach, including:
- The threat of ransomware-as-a-service (RaaS)—DarkSide ransomware operates as RaaS, meaning cybercriminals subscribe to their tools to execute ransomware attacks. This is significant because, in the past, hackers had to have coding expertise to be successful. With RaaS, however, users don’t need to be skilled or experienced to carry out sophisticated attacks. RaaS empowers novice hackers by providing them with an easy-to-use system for deploying ransomware.
- The impact of double extortion—Double extortion increases the stakes of a ransomware attack. Rather than only deleting data if the ransom isn’t paid, cybercriminals threaten to leak it. Since Colonial Pipeline did have backup data available to them, it would have been possible to wipe and restore their infrastructure without paying the ransom. However, they paid the ransom to keep their data from being exposed.
- The risks posed by aging infrastructure—Old and obsolete operating systems may be easier for cybercriminals to infiltrate. By exploiting vulnerabilities in the outdated network, cybercriminals can gain access to sensitive data and hold it for ransom.
Preventive Measures
Organizations can take the following actions to ensure that ransomware attacks don’t compromise their operations and data:
- Conduct a security risk evaluation. Take time to identify which critical systems and assets are most appealing to cybercriminals. By doing this, businesses can get a better idea of how to prioritize protection.
- Keep systems up to date. Update operating systems, applications and software regularly. Applying the latest updates improves systems, fixes problems and corrects any security issues discovered by developers.
- Maintain data backups. The Multi-State Information Sharing and Analysis Center reports that backing up important data is the most effective way for organizations to recover from a ransomware attack. Backups should be stored offline, out-of-band or in a cloud service so attackers can’t target them. They should also be tested regularly for efficacy.
- Train the team. Some of the most damaging cyberattacks occur due to human error. Training employees on the importance of cybersecurity and how to identify scams can help organizations reduce the likelihood of becoming a victim of ransomware attacks.
- Install antivirus software. Antivirus software protects against many cyberthreats, including viruses, spyware, malware, Trojans, phishing attacks, rootkits and spam attacks.
If an attack occurs, organizations should have an incident response plan ready with defined roles and communications that can be shared during an attack. Organizations that are overly cautious and plan proactively may be able to minimize damage.
Consider a Stand-Alone Ransomware Insurance Policy
Since cyber insurance isn’t standardized, organizations should review all policy language with one of our insurance advisors before choosing a plan that effectively covers ransomware. Policies can vary significantly in their language and coverage options, so we recommend policies that—at the very least—provide coverage for extortion demands and payments, as well as lost income resulting from an attack.
Organizations should also take a close look at the following definitions, terms and conditions when choosing a policy:
- Sublimits and deductibles—Most policies set a sublimit for covering ransomware. It’s important to review this limit carefully, considering that demands may start on the low side, but can increase quickly. Also, since making a ransom payment may make organizations a target for subsequent ransom demands within the policy year, the deductible amount should reflect that risk.
- Payment terms—Most policies require prior written consent before the insured can pay any ransom. This can result in payment delays and increased demands by the hackers. If an organization pays a ransom in order to resume business, without prior written consent by the insurer, there’s a chance that it may not be reimbursed. Therefore, organizations need to be comfortable with a policy’s terms in order to avoid compromising coverage.
- Definition of extortion—It’s important for organizations to fully understand and agree with their insurance company’s definition of extortion, since the definition dictates the trigger for coverage. For example, although hackers may intend to sell or misuse information, the ransom demand may only involve a countdown timer and demand for money. While the combination of the two may seem like an obvious threat to the insured, a carrier could possibly deny coverage on the basis that there was no explicit threat to sell or misuse information—all because of its unique definition of extortion.
What to Look for in a Policy
Companies should look for ransomware coverage that uses broad terminology and protects against a wide range of threats, including threats to do the following:
- Access, sell, disclose or misuse data stored on your network, including digital assets
- Alter, damage, or destroy software or programs
- Introduce malicious software, including viruses and self-propagating code
- Impair or restrict access. Look for policies with broad terms like, “threats to disrupt business operations”
- Impersonate the insured in order to gather protected information from its clients, also known as pharming or phishing
- Use your network to transmit malware
- Deface or interfere with your company’s website
The Importance of Risk Management
Ransomware insurance is most effective when coupled with a proactive risk management program, as there are many components in the fight against cyber crime. Business owners should work with one of our licensed advisors to review all applicable options before choosing cyber coverage.
Don’t let ransomware—or any type of cyber exposure—threaten your business.
Contact CoverLink Insurance today to learn more about available cyber policies and effective risk management techniques to protect your organization from ransomware attacks.
If you’d like additional information and resources, we’re here to help you analyze your needs and make the right coverage decisions to protect your operations from unnecessary risk. You can download a free copy of our eBook, or if you’re ready make Cyber Liability Insurance a part of your insurance portfolio, Request a Proposal or download and get started on our Cyber & Data Breach Insurance Application and we’ll get to work for you.