On Aug. 31, 2025, British automotive manufacturer Jaguar Land Rover (JLR) was hit by a major cyberattack that halted production and compromised critical IT systems and company data. The attack disrupted the production of tens of thousands of vehicles, leaving dealerships in multiple markets with low stock, delayed deliveries and parts shortages that forced customers to endure long waits for new orders and certain critical repairs. The breach tested the resilience of global logistics networks and underscored how a single cyber incident can strain supply chains, disrupt operations and erode business continuity.
Fortunately, organizations can learn valuable cybersecurity lessons by reviewing the details of this incident, its impact and the contributing factors.
The Details: Jaguar Land Rover Cyberattack
On Aug. 31, 2025, JLR IT teams began to notice erratic system behavior, raising concerns of a possible cyberattack. By early September, JLR had confirmed unauthorized access and proactively shut down key networks to contain the incident. The shutdown forced the closure of UK assembly plants, including those in Solihull and Halewood, with staff instructed to stay home. Production lines remained idle for weeks, resulting in significant operational and financial disruptions. The disruption inflicted approximately £1.9 billion ($2.5 billion) in total economic impact across the UK, including effects on JLR, suppliers and related industries, making it one of the costliest cyber incidents in British history.
The cyberattack severely affected JLR’s supply chain, leaving thousands of suppliers across the globe unable to process orders and disrupting parts production, logistics and aftermarket services. While the attack primarily affected UK-based systems, the interconnected nature of JLR’s global supply chain meant that disruptions quickly cascaded overseas. Suppliers and service centers in the United States and other markets faced part backlogs, delayed repair timelines and frustrated customers.
Although JLR did not formally confirm the source of the breach, a cybercriminal group known as Scattered Lapsus$ Hunters has since publicly claimed responsibility for the attack. Industry sources have speculated that the attackers may have gained entry using stolen employee credentials and that inconsistent access controls may have enabled the group to move laterally across JLR’s global network.
The Impact: Jaguar Land Rover Cyberattack
More than 30,000 employees and around 200,000 supply chain workers, dealerships and retailers worldwide were affected when a single breach in the UK brought JLR’s manufacturing to a standstill. The incident underscores the critical importance of thoroughly vetting supply chain risks, enforcing robust cyber hygiene measures and implementing resilient business continuity strategies to safeguard against global supply breakdowns.
The JLR cyberattack had significant and far-reaching consequences. Ramifications included the following:
Operational Disruptions
The cyberattack affected JLR’s global ordering, logistics and inventory systems. Consequently, dealerships faced delays in vehicle deliveries, while logistics networks struggled with canceled and postponed shipments. Customers endured extended wait times, and service centers reported shortages of replacement parts that hindered repairs.
Financial Losses
Globally, the attack cost JLR approximately £200 million (around $268 million) in direct expenses and contributed to a quarterly loss of roughly £485 million (around $652 million). For dealerships and supply chain partners, the financial impact was also significant. Halted production led to vehicle shortages, resulting in missed sales opportunities. Furthermore, organizations were compelled to consider costly contingency measures (e.g., expedited shipping and increased logistics costs to rush vehicles once production resumed) to minimize delays and maintain customer confidence.
Reputational Damage
Although the attack originated in the UK, its ripple effects were felt across global markets, where delays and parts shortages eroded confidence in JLR’s service reliability. Media coverage emphasized the scale of the disruption, raising concerns about the company’s preparedness and highlighting the reputational risks that follow operational breakdowns.
Regulatory Implications
The incident drew attention from regulators and industry bodies worldwide. It reinforced broader concerns about cybersecurity standards across manufacturing operations and supplier networks. It also highlighted the growing concern about operational technology vulnerabilities, which can expose critical systems to attacks and cause cascading effects across global production networks.
Lessons Learned: Jaguar Land Rover Cyberattack
There are several key takeaways from the JLR cyberattack regarding cybersecurity and operational resilience. The incident emphasized these important lessons:
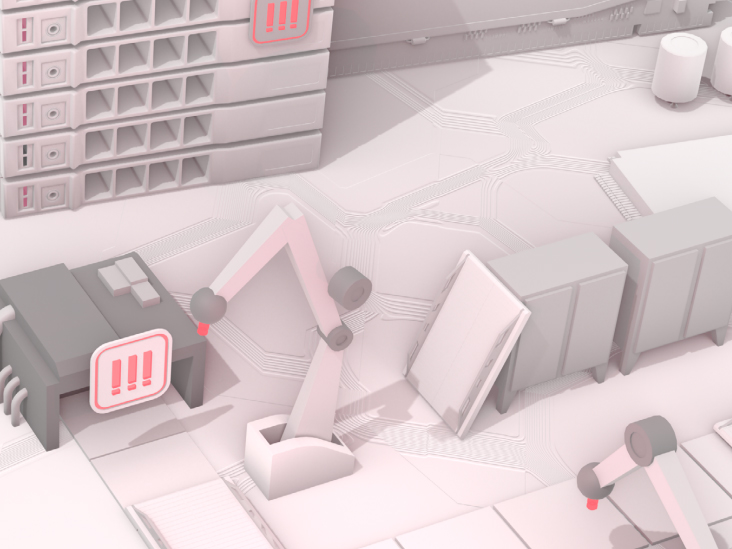
Importance of Segmentation and Zero-trust Security
JLR’s reliance on highly integrated IT systems, including factory automation and logistics, amplified the cyberattack’s impact. While this design maximized efficiency, it allowed attackers to move laterally, affecting multiple plants and systems simultaneously. Organizations can mitigate this risk by dividing their network into smaller, isolated segments, each with its own access controls—a process known as network segmentation. Organizations should also consider the merits of a zero-trust security model, which assumes no user or device has automatic trust and requires continuous verification of identity and access privileges, even for those already within the network.
Credential Management
Attackers were able to use stolen credentials from as early as 2021 to breach JLR’s systems and navigate across environments, according to industry reports. To prevent unauthorized access, organizations should implement robust credential lifecycle management, including regular password rotation, removal of unused or dormant accounts and regular password health audits to detect weak or exposed credentials. Multi-factor authentication, which was reportedly found to be inconsistent at JLR, should be enforced across all accounts for additional protection.
Third-party and Supply Chain Risk Management
The JLR cyberattack underscored the interconnected nature of modern supply chains and the cascading impact a single breach can have across multiple companies. Organizations must treat third-party risk as a core component of their cybersecurity strategy. To strengthen resilience, they should evaluate suppliers based on security controls and incident response capabilities, embed cybersecurity obligations into supplier agreements and implement tools and processes to monitor supplier networks for indicators of compromise.
Operational Resilience Planning
The attack revealed how quickly production and logistics can grind to a halt when core systems are compromised. Organizations should review their business continuity plans to ensure they are positioned to withstand severe disruptions. Plans should include manual workarounds to keep essential operations running when digital systems fail, as well as clear communication strategies to inform employees, customers and partners during a crisis.
Insurance Considerations
The financial scale of the attack underscored the importance of robust insurance coverage for operational outages, including those caused by disruptions from upstream suppliers. Organizations should review their cyber insurance policies and consider adding contingent business interruption (or CBI) coverage to protect against scenarios where a supplier outage impacts their operations.
We Can Help
If you’d like additional information and resources, we’re here to help you analyze your needs and make the right coverage decisions to protect your operations from unnecessary risk. You can download a free copy of our eBook, or if you’re ready to make Cyber Liability Insurance a part of your insurance portfolio, Request a Proposal or download our Cyber & Data Breach Insurance Application and we’ll get to work for you.